What is VAPT?
VAPT stands for Vulnerability Assessment & Penetration Testing. It is a security testing to identify security vulnerabilities in an application, network, endpoint, and cloud. Both the Vulnerability Assessment and Penetration Testing have unique strengths and are often collectively done to achieve complete analysis. Vulnerability Assessment scans the digital assets and notifies organizations about pre-existing flaws. Penetration test exploits the vulnerabilities in the system & determines the security gaps.
Why would your organization need VAPT?
Vulnerabilities exist in all levels of a computing system (on-premise and cloud) regardless of the organization’s size. There’s a big misconception that small and medium-sized businesses are spared by cyber attackers. But this is far from reality. As the security of small businesses is usually relaxed, attackers incline towards them. Many times, organizations say they don’t require vulnerability risk assessments because they’re such a small organization. But this false belief could prove very costly for a business, big or small – SME or MNC. The security loopholes in your IT infrastructure are:

-
 Poor Hardware & Software Design
Poor Hardware & Software Design -
 Complex Software & Hardware
Complex Software & Hardware -
 Poor Authentication System
Poor Authentication System -
 Misconfigured System
Misconfigured System -
 Unsecured Network
Unsecured Network -
 Vulnerable Endpoints
Vulnerable Endpoints
Strengthen your defences with Inspirisys VAPT
- Identify The Security Loopholes
- Improve Cyber Resilience
- Avoid Data Breaches
- Inspect Network Defence System
- Protect Organizational Data
- Comply with Security Standards

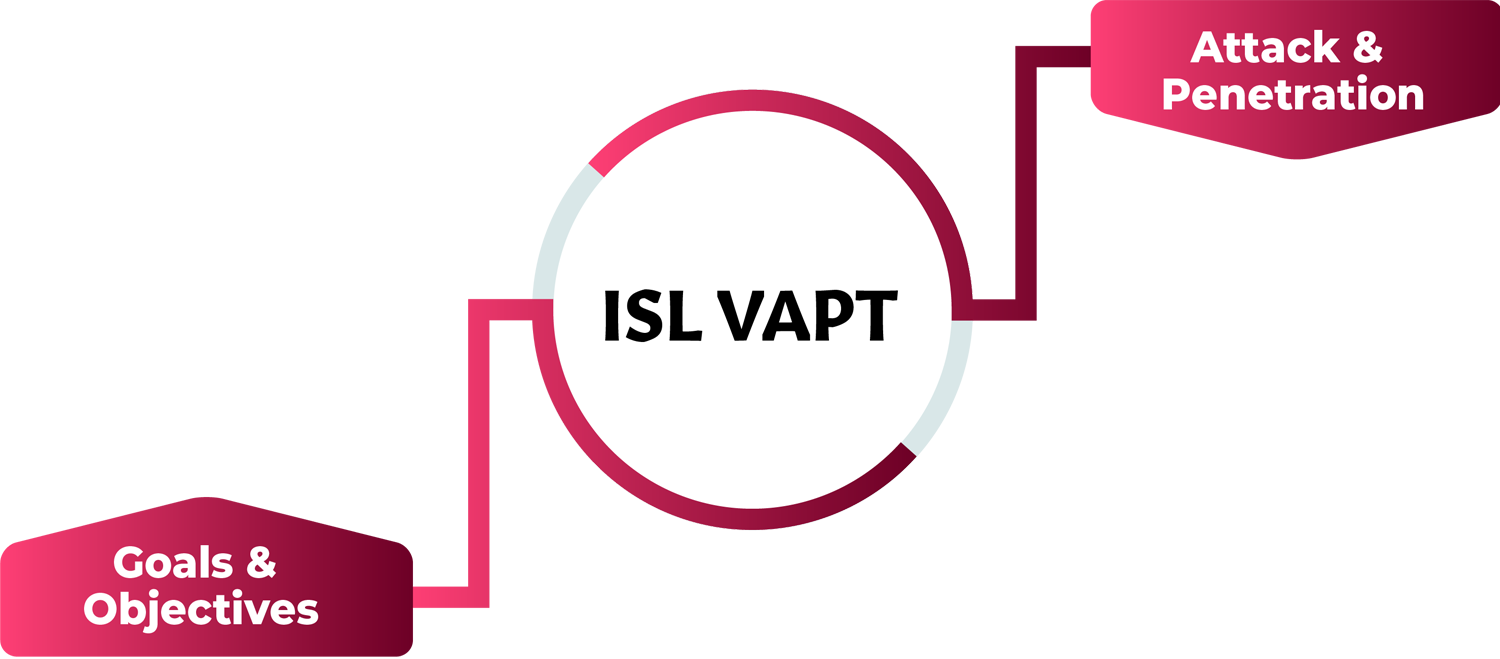
How It Works



VAPT as a Service

 Application VAPT
Application VAPT
As organizations are moving their critical data and functions to web & mobility platforms like iOS and Android mobile applications, the organizational data is exposed to cyber actors. With applications VAPT, we support your enterprise to identify vulnerabilities.

 Network VAPT
Network VAPT
Network VAPT is to identify potential vulnerabilities in the network that cyber actors may exploit. Inspirisys delivers a prioritized list of vulnerabilities identified in your network that can help you to line-up the mitigation strategies to stay ahead of cyber-attacks.

 Endpoint VAPT
Endpoint VAPT
Future proof your endpoints with a complete vulnerability analysis that identifies security gaps. We evaluate security risks in the endpoints which include desktops, laptops, smartphones, tablets, servers & workstations to prioritize vulnerabilities and support your future security strategies.

 IoT VAPT
IoT VAPT
The rapid adoption of Internet of Things technology opens the opportunity for cyber threats to exploit the connected systems. IoT devices are not limited to devices. It comprises IoT field gateways, databases, applications, servers etc. With deep domain expertise, we assess vulnerabilities across the IoT ecosystem.
Why Choose Inspirisys?
- 25 Years of expertise in the security landscape
- Excellent track record of providing defensive cybersecurity solutions
- Complete Security Assessment – Applications, Network, Cloud, Endpoints
- Pen Testers with Specialised Expertise in Cyber Security Landscape
- Automated Testing to ensure maximum quantities of vulnerabilities are discovered
- Effective Gap Analysis by Security Experts
- In-depth approach to provide a holistic report
- Reports with Risk Rating Scale
- Post-test consultation for risk mitigation action plans





