A Security Operations Center (SOC) plays an important role in helping organizations manage the growing complexity of their digital environments. As businesses rely on interconnected systems, cloud platforms and distributed networks, maintaining visibility into security events has become essential for protecting critical systems and data.This article explains what a Security Operations Center is, the role it plays in organizational security and the key elements that support its day-to-day functioning.
What is a Security Operations Center (SOC)?
A Security Operations Center (SOC) is a centralized function where security professionals oversee and manage security-related activities across an organization’s IT environment. It brings together skilled personnel, operational processes and specialized technologies to analyze system activity, investigate suspicious behavior and handle security incidents when they arise.
Within this environment, the SOC team reviews data from multiple systems, evaluates potential weaknesses and ensures that existing protections are functioning effectively. Along with responding to incidents, the it also contributes to improving security controls and strengthening the organization’s ability to manage evolving cyber risks.
Why is a Security Operations Center Important?
Modern IT environments generate large volumes of system activity across networks, applications, servers and connected devices. Analyzing this activity through isolated tools or manual review can make it difficult for organizations to identify threats quickly or understand the broader security implications of unusual behavior.
One of the key reasons organizations rely on a SOC is the growing sophistication of cyber threats. Attack techniques have evolved to include multi-stage intrusions, automated exploitation, and attempts to remain undetected for extended periods. Structured security oversight enables organizations to examine abnormal patterns, evaluate potential vulnerabilities, and limit the impact of malicious activity.
A SOC also supports regulatory and compliance obligations that require organizations to maintain strong monitoring, incident management, and data protection practices. By strengthening visibility into system activity, it helps organizations safeguard critical information assets while maintaining the stability of essential business systems.
Key Components of a Security Operations Center
The effectiveness of a Security Operations Center (SOC) depends on three foundational elements: people, processes and technologies. Together, these components enable organizations to manage security activities systematically and maintain consistent oversight of their digital infrastructure.
People
A typical SOC team includes analysts who inspect unusual system behaviour, engineers who maintain monitoring infrastructure and incident responders who manage active security events. Each role contributes to maintaining operational readiness and ensuring that emerging threats are scrutinized and handled efficiently. Continuous skill development and industry certifications are also important, as security teams must adapt to evolving attack techniques and technologies.
Processes
Clearly defined procedures establish how alerts are analyzed, when incidents are escalated and how responses are coordinated across teams. Structured SOC workflows help ensure consistency in investigations and reduce delays during critical situations. Processes also include documentation, reporting practices and adherence to regulatory requirements related to data protection and risk management.
Technology
Security technologies provide the visibility and analytical capability needed to monitor complex IT environments. Many organizations rely on platforms such as a SIEM platform, endpoint detection systems, and other SOC tools that collect and analyze event data from multiple sources. These technologies support event correlation, security analytics and centralized monitoring through a unified SOC dashboard. Security Automation capabilities are increasingly integrated into modern environments, enabling routine investigative tasks to be handled more efficiently while allowing analysts to focus on complex security incidents.
Types of Security Operations Centers
Organizations implement different SOC models depending on their security requirements, internal expertise, and operational scale. These models define how security monitoring and incident management responsibilities are structured.
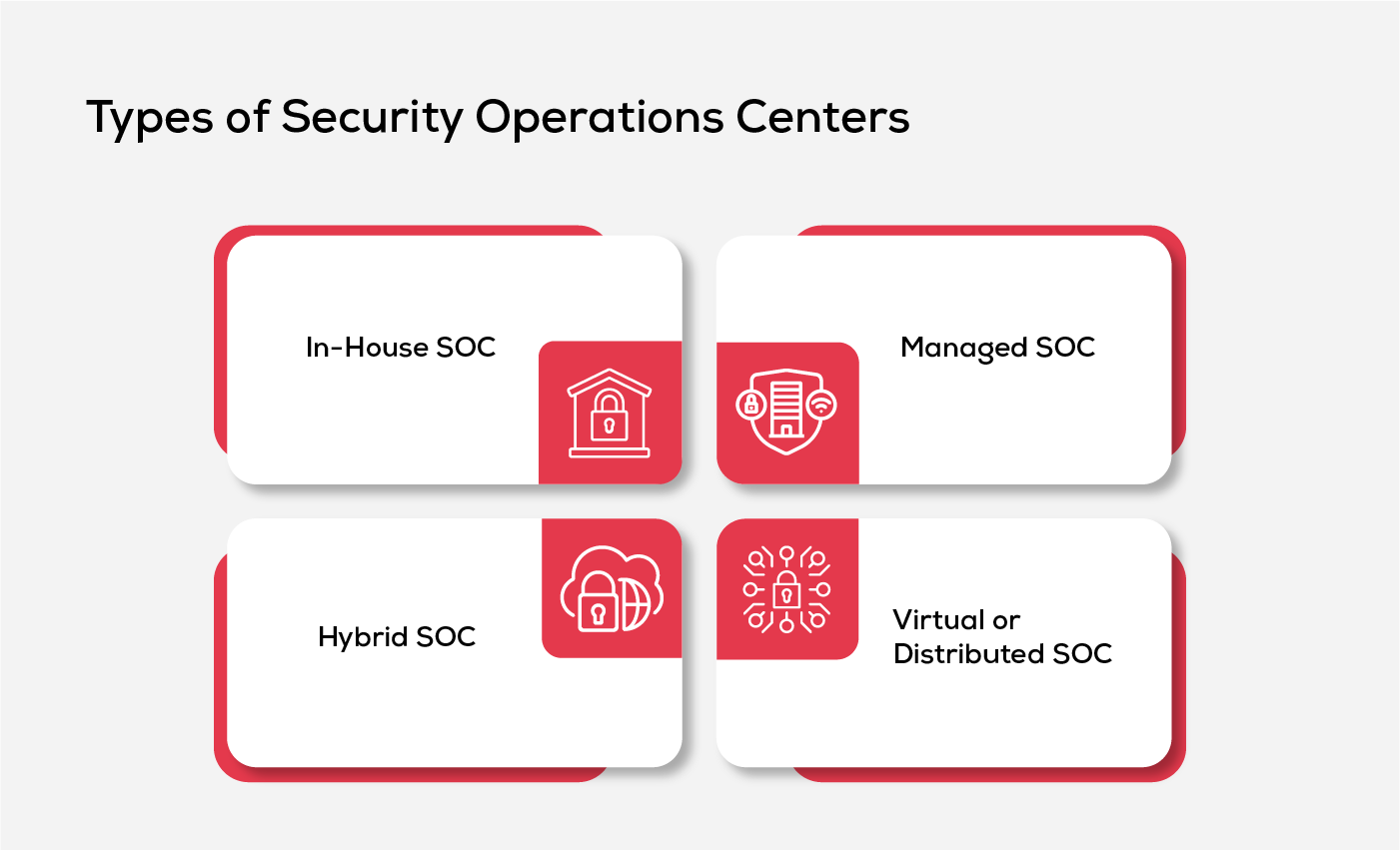
In-House SOC
An in-house Security Operations Center is built and managed internally by the organization. The security team, infrastructure and monitoring systems are maintained within the company’s own environment. This model provides greater control over security operations, data handling, and response procedures. It is typically adopted by large enterprises with the resources and expertise required to maintain dedicated security teams and supporting technologies.
Managed SOC
A managed SOC is operated by an external security provider that monitors and manages an organization’s security environment remotely. In this model, specialized teams handle threat monitoring, alert investigation, and incident response on behalf of the organization. Managed services are often chosen by companies that require continuous security oversight but do not have the resources to maintain a full internal security operation.
Hybrid SOC
A hybrid SOC combines internal security teams with external monitoring support. Organizations maintain internal oversight while partnering with external providers for additional expertise, extended monitoring coverage or specialized threat analysis. This model allows organizations to balance operational control with access to broader security capabilities.
Virtual or Distributed SOC
A virtual SOC operates through distributed teams and cloud-based security platforms rather than a single physical location. Analysts may work from multiple locations while accessing centralized monitoring systems and security tools. This model supports scalability and allows organizations to maintain constant monitoring across geographically distributed environments.
Key Functions of a Security Operations Center
Several operational responsibilities support the day-to-day functioning of a SOC and help maintain the effectiveness of organizational security controls.
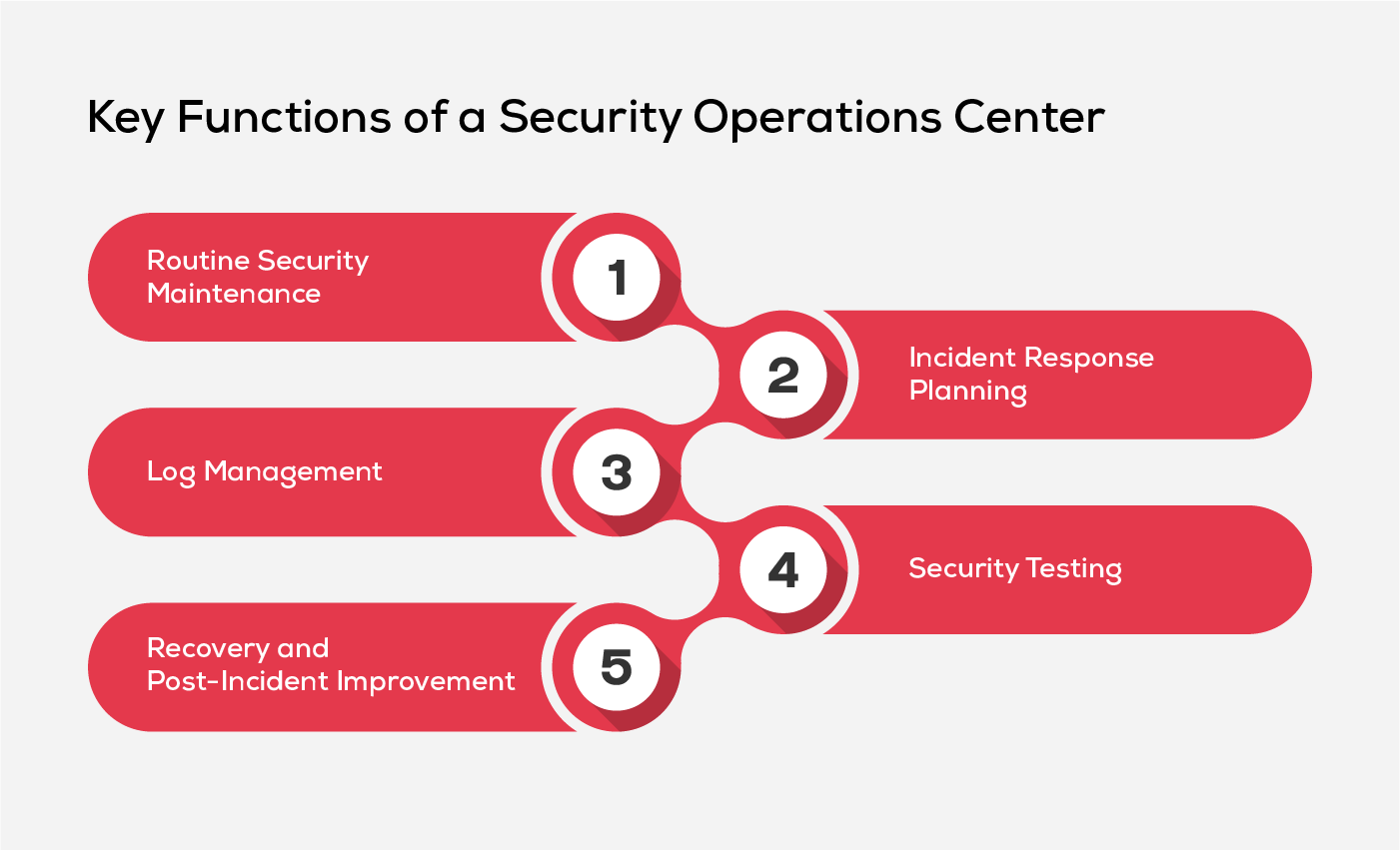
Routine Security Maintenance
Security systems require regular maintenance to remain effective. This includes applying software patches, updating firewall configurations, reviewing security policies and ensuring tools remain properly configured. Preventive maintenance reduces the likelihood of vulnerabilities being exploited and helps sustain consistent protection across the environment.
Incident Response Planning
SOC teams develop structured response plans that define roles, escalation procedures and response workflows. These plans provide clear guidance during security incidents and help teams coordinate actions quickly.
Log Management
Large volumes of system logs are generated across IT environments. Collecting and analyzing this information allows security teams to establish normal activity patterns and identify anomalies that may indicate malicious behavior. It improves investigation capabilities and supports faster identification of suspicious activity.
Security Testing
With regular testing, organizations identify weaknesses before attackers can exploit them. Activities such as vulnerability assessments and penetration testing allow teams to evaluate existing defenses and strengthen security measures where gaps are discovered.
Recovery and Post-Incident Improvement
Once a security incident has been contained, systems must be restored and normal operations resumed. Recovery activities involve restoring systems from backups, resetting credentials and verifying system integrity. Teams also conduct post-incident analysis to identify root causes and refine processes and security controls to prevent similar issues in the future.
Benefits of a Security Operations Center
Establishing a SOC brings measurable operational and strategic advantages to an organization’s security framework. The following benefits highlight how a structured SOC capability strengthens coordination, and long-term security management.
Centralized Security Visibility
SOC provides a consolidated view of security activity across multiple systems and tools. This centralized visibility allows organizations to understand security conditions across their environment without relying on fragmented monitoring systems.
Improved Alert Prioritization
Security environments often generate a high volume of alerts that require evaluation. A SOC helps categorize and prioritize these alerts so that the most critical risks receive attention without overwhelming security teams.
Greater Operational Consistency
Structured operational workflows ensure that investigations and security procedures follow defined standards. This improves reliability in how security issues are handled across different teams and operational scenarios.
Stronger Cross-Team Coordination
Security investigations frequently require collaboration between security teams, infrastructure administrators and application owners. SOC provides a central point for coordination, helping teams exchange information and resolve security issues more efficiently.
Better Strategic Security Planning
Operational data collected through SOC activities provides insights into recurring security issues and system weaknesses. These insights help organizations make informed decisions when strengthening controls and planning future security initiatives.
Best Practices for an Effective Security Operations Center
Maintaining an effective Security Operations Center (SOC) requires more than tools and personnel. Consistent operational practices help ensure that monitoring, investigation and response activities remain aligned with organizational priorities and evolving threat conditions.
Align SOC Strategy with Business Objectives
Ensure that security operations support broader business priorities. Conducting risk assessments helps identify critical assets and evaluate the potential impact of cyber incidents on business operations. Clear metrics and performance indicators also help demonstrate how SOC operations contribute to protecting organizational systems and supporting business continuity.
Establish a Well-Integrated Security Tools Stack
Deploy security technologies in a deliberate and coordinated manner instead of relying on a large collection of disconnected tools. Integrated security platforms also make it easier to manage alerts, analyze system activity and maintain consistent situational awareness through a unified SOC security platform.
Leverage Threat Intelligence and Advanced Analytics
Incorporate reliable threat intelligence sources and advanced analytical capabilities to improve the ability to identify emerging threats. Machine Learning and security analytics technologies can help analyze large volumes of system data and highlight patterns that may indicate malicious activity. These capabilities assist analysts in identifying risks earlier and prioritizing investigations effectively.
Maintain End-to-End Network Visibility
Ensure that security teams have visibility across the entire IT environment, including cloud infrastructure, on-premise systems, and distributed endpoints. Unified monitoring interfaces and consolidated SOC dashboards help analysts review activity without relying on multiple disconnected systems. Strong visibility enables analysts to identify suspicious behavior across different parts of the network more effectively.
Maintain Continuous Security Monitoring
Establish the capability to monitor systems continuously, as security threats can emerge at any time. Continuous SOC monitoring allows analysts to identify abnormal activity and investigate potential threats without delay. This operational readiness helps organizations limit the potential impact of malicious activity within their environment.
Future of Security Operations Centers
Security operations are increasingly evolving toward automation-driven and intelligence-led environments. Technologies such as security orchestration, automation, and response (SOAR) platforms, along with AI-powered security analytics, are helping SOC teams process large volumes of security data more efficiently. These capabilities reduce manual effort, improve investigative speed and allow analysts to focus more on complex threat analysis and proactive security activities.
Operational models are also becoming more flexible as organizations explore managed SOC and SOC-as-a-Service (SOCaaS) approaches. These models provide access to advanced expertise and scalable monitoring capabilities without the need to maintain a fully staffed internal operation. As digital infrastructures expand and threats become more sophisticated, SOC environments are expected to rely more heavily on automation, data-driven analysis, and proactive threat detection strategies.
Inspirisys Security Operations Center Services
At Inspirisys, we help organizations strengthen their Security Operations Center (SOC) capabilities with managed security services designed to support modern IT environments. Our team works alongside enterprise security teams to help improve operational readiness, strengthen security monitoring practices and manage evolving cyber risks more effectively.
With deep experience in enterprise infrastructure and cybersecurity services, we support organizations in building resilient SOC operations that align with their security and compliance requirements.

Frequently Asked Questions
1. What is Root Cause Analysis in a Security Operations Center (SOC)?
Root cause analysis is the process of identifying the underlying reason behind a security incident. SOC teams use it to understand how an incident occurred and implement measures to prevent similar issues in the future.
2. Who works in a Security Operations Center (SOC)?
A Security Operations Center (SOC) includes several specialized roles that work together to manage security operations. These typically include SOC analysts (Tier 1, Tier 2, and Tier 3) who monitor alerts and investigate suspicious activity, security engineers who maintain and optimize security tools, incident responders who handle active security incidents, and threat hunters who proactively search for hidden threats within the environment.
3. How does a Security Operations Center (SOC) work with other departments in an organization?
SOC teams collaborate with IT, infrastructure, and application teams to investigate security issues and implement remediation actions. This coordination helps ensure that threats are addressed while maintaining system functionality and business operations.
4. Can small businesses benefit from a Security Operations Center (SOC), or is it mainly for large enterprises?
Small and mid-sized businesses can also benefit from SOC capabilities, especially through managed SOC services. This allows them to access professional security monitoring and expertise without maintaining a full in-house security team.
5. What is the difference between a Security Operations Center (SOC) and a Network Operations Center (NOC)?
A SOC focuses on detecting, analyzing, and responding to cybersecurity threats. A Network Operations Center (NOC) is responsible for maintaining network performance, availability, and infrastructure stability.







